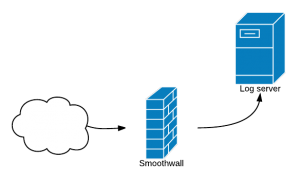
Firewall Project, Proxy and Syslog.conf anno 2013
This is so long ago but is it is still shareable and it is fun to see the progress that I have made in made short time as an IT.
Introductions
Back when I was studying we worked on a firewall project with Smoothwall. In my opinion a strong , customize firewall solution. Running on a dedicated machine or VM´s with minimum 2 nics.
Have been working with this open source firewall called Smoothwall 3.0 Express. A bit of a quite cool piece of software. There is a lot of possibilities for customizing firewall setup with user made mods. These mods that is found in the community section of the Smoothwall site is well documented.
We chosen Smoothwall of the blue. There were really no research for picking the firewall. But at the moment im glad we did. We have had some problems, not big but is has been learn by doing. First, remember the the password you chose for the root. Second, type the right name for the firewall. We had been hearing about this IPSec and 2 minutes after our firewall was called IPSec-firewall instead of ITseC-firewall. It good that it is a fast installation. Takes roughly 10 minutes for a install.
Getting IP’s and hostnames where quite easy. Because we are in the schools network we have some limitations when it comes to accessing the Internet and our service running behind our firewall.
Faced a problem when the proxy wasn’t what expected. The proxy was be used for the internal web traffic. The Smoothwalls web proxy, linked for use for a remote proxy server. Unusable for the project as it did not meet the requirements set. It is here where the mods come into play. A proxy mod called AdvProxy it a great little piece of software, we thought.
Proxy
Installed by using a SSH connection on port 222 and this is what is a nice little feature for obscurity security.
Well I´m smarter now on know this would not work that much now.
ADVproxy
ssh -l root@itsec-firewall -p 222
Password: *********
The file was transffed by “Transport”, Well Transport for mac, its like Winscp for windows. But at this time I was really a command line noob. Well still am but its getting better .
Unpacked the file with
tar -xzf smoothwall-advproxy-3.0.6.tar.gz
And installed by command
Smoothwall-advproxy/install
After this I got a feel for it and wanted to add more mods. Firewall log was a mess. It with only a server and a client where was to much traffic to go though. By the same principle as the advproxy, a enhanced firewall log mod. This mod sorted the traffic and divided into green and red as the two interfaces used for incoming and outgoing traffic. And a possibilities to block IP’s on the fly.
A more advanced IDS called guardian was installed as well. Together with Snort and Oink code this should be good solution.
This advproxy – Dont use it. The proxy will not work after it is installed. This folders are not placed in the right path.
Smoothwall proxy
For configering the proxy
var/smoothwall/proxy/acl
This path is where the proxy can be used for much more than, as a URL filtering proxy or IP filtering. In this project URL filtering is being chosen for implement restrictions on what pages the client is allowed to see. This acl file updates the Squid.conf file that is the proxy config file. But because not to implement something that is half done or on the fly. All the configuration is made and after the proxy restarts, the changes are implemented. This will minimize the downtime to zero when configuring.
All URL filtering are down addition of this line of code
acl blocked_sites url_regex “/var/smoothwall/proxy/badsites.txt
http_access deny blocked_sites
A text file containing the sites for blocking are placed in the proxy folder and linked to it.

As far as the project is now it is looking good for meeting the deadline in 5 weeks.
The next task is to use a SSH tunnel to connect to the VNC server instead of the normally port 5900. So again security by obscurity. Though VNC already use a 128bit encryption and together with a SSH tunnel it should be safe from the most intruders. VNC uses the windows server user information for log on and the administrator has been removed because of this. Because that is the first login the Hacker will try. I dont know how to make the SSH connection yet with my mac but in windows putty is being used as tunnel software. redirecting to the right port.
Syslog Exporting
On the windows server there runs a program as a service. This means that it is running without anyone needs to be log into the system. This program is KIWI SYSLOG. and this program listen to request from the firewall.
Taking a look at the config file /ect/syslog.conf
Here we can pick and choose that logs that will be presented by the Kiwi syslog on the server. At the moment the logs are saved on the Smoothwall machine. E.g kern.* is saved at location /var/log/kernel. If decided to export the Kernel logs the path name are change to @192.168.0.2.
Smoothwall is configured to broadcast following:
- authpriv.*
- mail.*
- *.emerg
- uucp, news.crit
- local7.*
If we choose Kern.* if will spam the log and will be totally useless. It will be hard to sort out real threats and issues. It will be like finding a needle in a hay stack.
To edit the config file I used ‘VI’ is used enter a edit mode. Then “I” for insert. Change what will have changed then “esc , :wq for save and exit.
KIWI SYSLOG DEAMON
Edited the syslog.conf file for sending firewall information to server for logging. KIWI Syslog is running as a service so event if there is no log on the program will monitor the traffic and alert in case of a intrusion,
kern.* @192.168.0.2 and it will will receive all from info to emergency
Therefor – Kern.crit @192.168.0.2 and it will not only send logs over critical. Snort.conf and guardian..conf have also been edited for sending there logs to KIWI Syslog.
KIWI SYSLOG Deamon is a free version of the much bigger and more capable but quit expensive. This program collect the syslog broadcast from Smoothwall and put it neatly in a text file for read or script to collect and sort out selective date.
Kiwi syslog deamon has the advantage to set up alarms to if a certain amount of hit by the firewall to send a email to system administrator. This was unfortunately not possible due to schools security policy.
In test it queued a email and tries 3 times to send, with 1 min pause in-betweens At this moment the alarm threshold is a 1500 hits pr. hour. It has been chosen to send the log hits to a plain text file, but it is possible to have it send to a database server.